In the light of recent aquisition of Twitter by Elon Musk, more and more people are migrating to Mastodon, a similar social media platform. Here are seven security risks that you should be aware before opening a new account on Mastodon.
What is mastodon?
Mastodon has been around since 2016 and is an open-source micro-blogging platform similar to Twitter. Here users submit “toots” instead of “tweets”, the length limit is increased from 280 to 500 characters and liking (mark as favorite) a post does not have much impact.
What really makes it different from Twitter is that anyone can host their own independent Mastodon server and admins are responsible to set it up, keep it running, managing the community and setting up the content rules. Even you can host a server and be an admin. In some ways similar to Reddit communities, except that the Mastodon servers are also hosted by the admins and there is nothing else above them.
While some servers allow anyone to be a member, other are either invite-only or require approval. mastodon.social was the first Mastodon server set up. It is currently crowdfunded and is kept alive through sponsorships and donations on Patreon. Other admins might choose to pay the hosting bills themselves or have a membership subscription. Regardless, someone has to pay one way or another.
Popular mastodon servers
- infosec.exchange – cybersecurity
- mstdn.social – general topics
- fosstodon.org – technology
- gensokyo.social – gaming
- mastodon.art – art
Mastodon (in)security
1. Impersonation and phishing
Because it is still quite a new platform and users with large follower-base on Twitter have not yet registered their “known” handle, the potential for impersonation is high. Combine this with the fact that Mastodon does not have a way of verifying user identities AND the fact that anyone can spin-up a server to register any handle they want.
All these can quickly become a recipe for disaster.
The main panels on the user interface dashboard are the Local and the Federated ones. The Local panel is where users see posts from people part of the same server. The Federated panel shows posts from other servers as well. As you can imagine, it’s on the Federated panel where you might end up seeing posts from hundreds of Donald Trump accounts, each that are part of other servers (good luck deciding which one is the real Donal Trump).
On top of that, it is also possible to follow and send DMs to people on other servers.
Obviously this could open the Pandora’s box on phishing and fake news, therefore sticking with the Local panel for the moment seems a safer bet. It is here where as admins can monitor the content and ban suspicious accounts.
2. information privacy
Another thing to keep in mind is that admins of a Mastodon server are in God mode. This means that they can see information about your account such as email, IP address, and read your “private” messages. While this should not come as a surprise since they are maintaining the infrastructure, it’s still good to keep it in your mind.
The DM option states that “Posts on Mastodon are not end-to-end encrypted. Do not share any sensitive information over Mastodon” – so expect less to no-privacy on your messages. Mentioning another user using their handle in a DM will add that user to the conversation. Keep this in mind before mentioning someone in a DM as they may pop-up unexpectedly.
3. Patches
Similar to any other self-hosted solution, the “product owner” has to ensure that security patches are deployed and CVEs are constantly monitored. Based on the server that you choose to join, the admins might be volunteers or have limited interested/expertise on ensuring that newest security patches have been installed.
Recently this week Gareth Heyes (@garethheyes) – researcher at Portswigger announced that he discovered a vulnerability in the servers using the Gitch fork of Mastodon. This allowed him to Steal passwords from infosec Mastodon – without bypassing CSP by abusing a HTML injection vulnerability. Keep in mind that this happened on the Information Security server which has a large community of cybersecurity professionals.
While this server might have been quickly patched and the issue remediated, this might not be the case with the other 1000 servers that are exposed on the internet. Make sure to check how to find mastodon servers on Shodan using the favicon hash down below in the article.
4. Denial of Service
When a hoard of 500,000 people decided to move from Twitter to the mastodon.social server in less than a week, it took the founders by surprise as not enough resources were available to sustain this huge influx. Their solution was to close down the registration and create a queue system.
Smaller servers can easily become targets of denial of service where botnets or even large communities decide to target them and quickly exhaust their resources.
While big social media platform such as Twitter, Facebook, Instagram have the resources to deal with such attacks, not the same can be said by a bunch of people who set up a Mastodon server as a hobby and use 5 server on an cloud instance.
5. Denial of Pocket
Similar to Denial of Server, a Denial of “Pocket” attack takes advantage of the automated scaling-up of resources set up by the administrators of the Mastodon server.
If the server is hosted on cloud and is configured to automatically request more resources when not enough are available, this could cause a large bill during a Denial of Service attack. While the DoS might not be successful, the bill at the end of the month can end up to be very expensive.
6. Man in the Middle
Successful Man in the Middle attacks happen where the communication between the clients and the server is not protected using encryption. It has been found that a large number of the Mastodon servers discovered on Shodan are either lacking TLS, or the certificates are self-signed.
Using such as server is highly discouraged as adversaries can intercept the communication, inject malicious payloads and run code in the context of the user session.
7. requests of your information
In certain situations, government entities might require the administrators to provide information about specific users. If you end up in such situations, there are probably more things to worry about however.. You should expect that government requests are handled with less resistance and less transparency compared to what you might be used from other social media platforms.
Social engineering attack on the administrators is another scenario where adversaries could gather information about an account by pretending to represent a governmental entity.
Finding mastodon servers on shodan
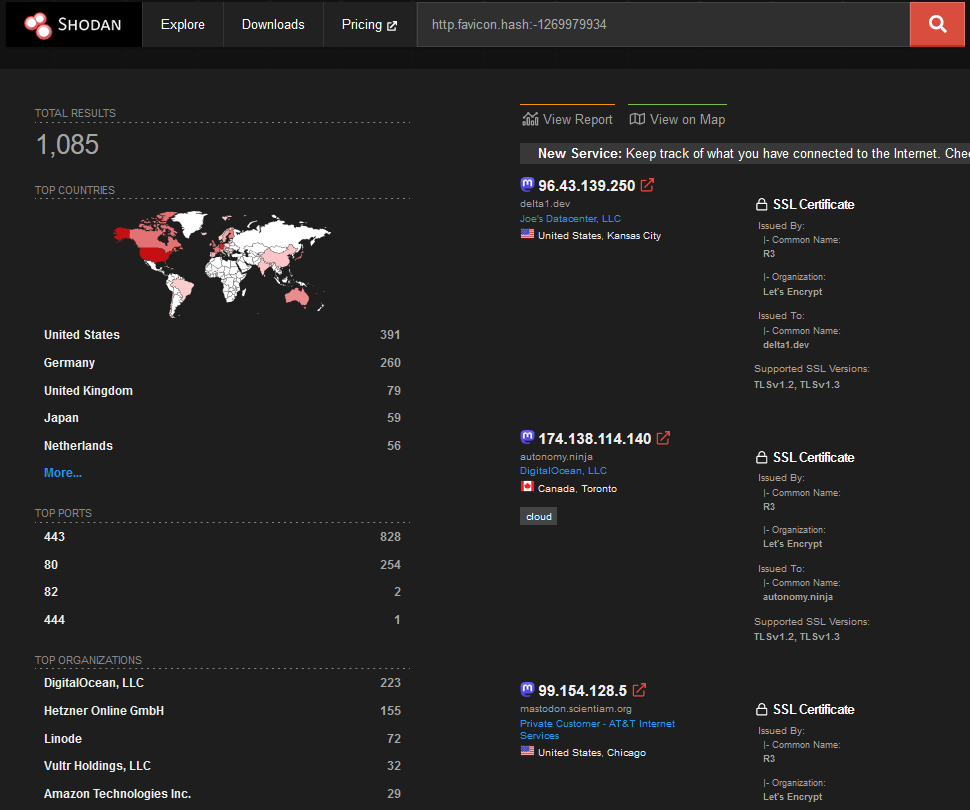
While searching for “Mastodon” on Shodan returned several results, I found that some of them where false positive. Using the http.favicon.hash filter (requires authentication but no subscription), it was possible to improve the the search results.
Using the following python3 script was possible to generate the mmh3 hash of the mastodon favicon
import mmh3
import requests
import codecs
response = requests.get('https://infosec.exchange/favicon.ico')
favicon = codecs.encode(response.content,"base64")
hash = mmh3.hash(favicon)
print(hash)
The following Shodan query was used resulting in over 1000 servers discovered
http.favicon.hash:-1269979934
setting up a mastodon server in less than an hour
References
- https://www.marketplace.org/2022/11/18/can-mastodon-replace-twitter-or-is-it-a-different-beast/
- https://www.intego.com/mac-security-blog/mastodon-safety-how-to-protect-yourself-from-security-and-privacy-risks/
- https://portswigger.net/daily-swig/mastodon-users-vulnerable-to-password-stealing-attacks
- https://portswigger.net/research/stealing-passwords-from-infosec-mastodon-without-bypassing-csp
- https://www.wired.co.uk/article/twitter-users-mastodon-meltdown
- https://www.thetealmango.com/technology/best-mastodon-servers-to-choose-when-you-join-the-twitter-alternative/